 88
88- 0
Top 5 Python Books You Must Read
This article provides a list of the top five Python books. I've read each book on this list, so I can guarantee for their excellence and level of knowledge.
- 0
Top 5 Linux Books You Must Read
This article provides a list of the top five Linux books. I've read each book on this list, so I can vouch for their excellence and level of knowledge.
- 0
Security Misconfiguration (Tryhackme)
The Security Misconfiguration vulnerability from Owasp Top 10 is explained in the article along with a Tryhackme demonstration.
- 0
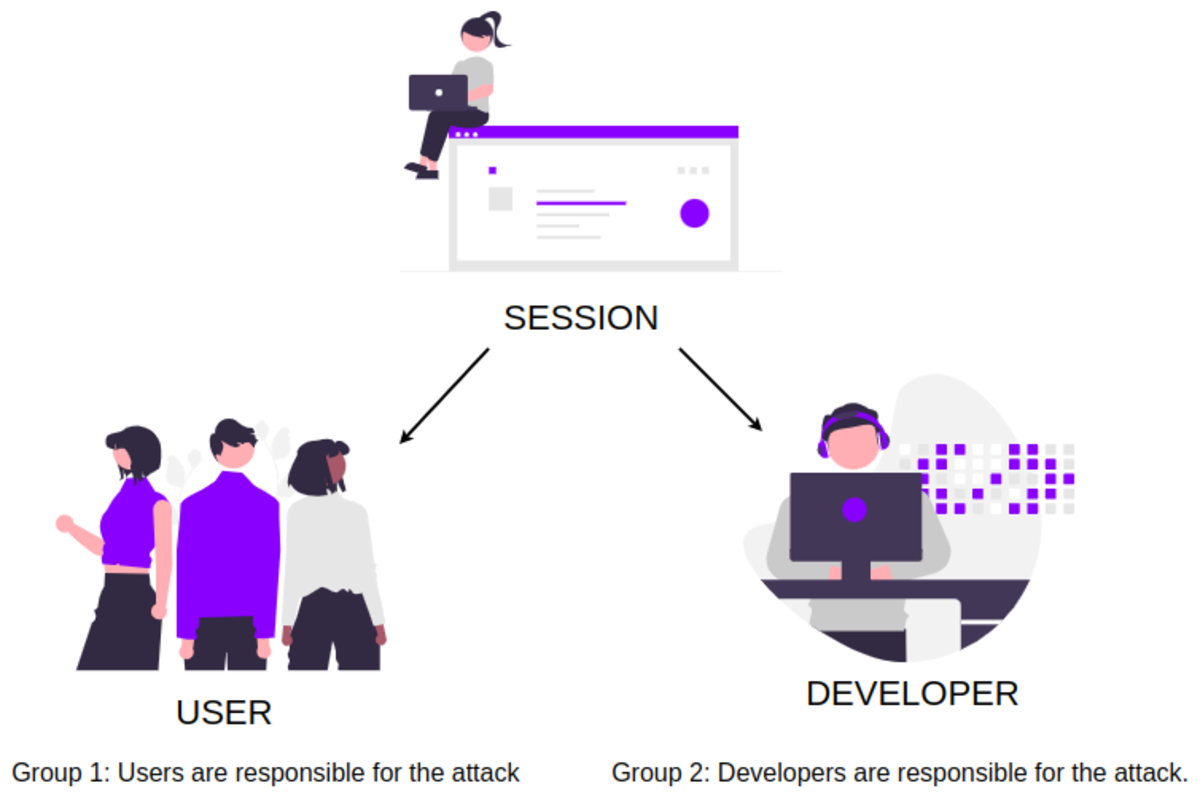
Broken Authentication (Tryhackme and Owaspbwa)
With examples from Tryhackme and Owaspba labs, the article describes broken authentication, one of the most critical Owasp Top 10 vulnerabilities.
- 0
Sensitive Data Exposure (Tryhackme)
This article explains the sensitive data exposure vulnerability along with an exercise from the Tryhackme platform.
- 0
Brute Force Attack (Owaspbwa Lab, Hydra Tool)
Introduction to brute force attacks using Burp Suite and Hydra following some practice problems of OWASPBWA Lab.
- 0
Command Injection (Tryhackme and Owaspbwa)
An in-depth guide on Command Injection web security vulnerability along with TryHackMe and OWASPBWA challenges for practice.
- 0
HTML Injection (Tryhackme and Owaspbwa)
The blog talks about the most easy-to-learn web security vulnerability HTML Injection.
- 0
Website Enumeration & Information Gathering [Part 1]
Learn about the first step of finding any vulnerability in a web application using google dorks and Linux commands like ping, host, and nslookup.
- 0
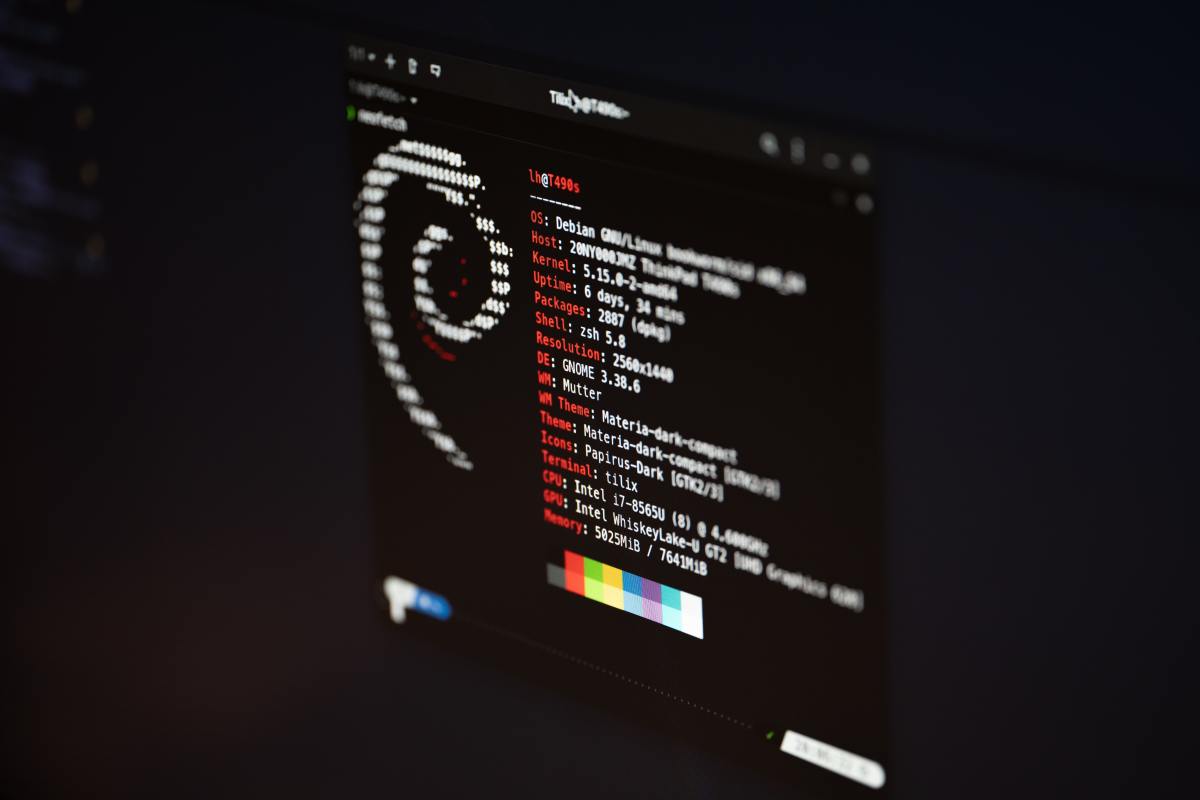
Website Enumeration and Information Gathering [Part 2]
This is part 2 of the Website Enumeration & Information Gathering article which talks about the first step of finding any vulnerability in a web application using Linux commands whatweb, nmap, and nikto.
- 0
Bug Bounty Hunting With Burp Suite (Intercept, Repeater & Intruder)
An introduction to the Burp Suite program and three of its primary features (Intercept, Repeater & Intruder).
- 0
Broken Access Control (Tryhackme and Owaspbwa)
This article provides you with the information you will need to complete the TryHackMe and OWASPBWA practice labs for Broken access control vulnerability.
- 0
30+ Standard Linux Commands for Beginner or Intermediate Users
These 30+ top Linux commands are selected to take you from a beginner to an advance/power user of Linux.






![Website Enumeration & Information Gathering [Part 1] Website Enumeration & Information Gathering [Part 1]](https://images.saymedia-content.com/.image/t_share/MTkzNDUxMzQzMTg3ODE0MDc3/website-enumeration-information-gathering-part-1.png)
![Website Enumeration and Information Gathering [Part 2] Website Enumeration and Information Gathering [Part 2]](https://images.saymedia-content.com/.image/t_share/MTkzNDUxMzQzNzI0NzUwMDUy/website-enumeration-information-gathering-part-2.png)